OpenSecurityTraining: Exploits 2: Exploitation in the Windows Environment (day 3, part 1)
Exploits 2: Exploitation in the Windows Environment
Creator: Corey K.
For more information and to download the training material visit: http://bit.ly/OST_EWE
Playlist Open Security Training: http://bit.ly/OST_playlist
This course covers the exploitation of stack corruption vulnerabilities in the Windows environment. Stack overflows are programming flaws that often times allow an attacker to execute arbitrary code in the context of a vulnerable program. There are many nuances involved with exploiting these vulnerabilities in Windows. Window's exploit mitigations such as DEP, ASLR, SafeSEH, and SEHOP, makes leveraging these programming bugs more difficult, but not impossible. The course highlights the features and weaknesses of many the exploit mitigation techniques deployed in Windows operating systems. Also covered are labs that describe the process of finding bugs in Windows applications with mutation based fuzzing, and then developing exploits that target those bugs.
Topics covered in the labs for this class include:
Exploiting a vanilla Windows stack overflow with no mitigations turned on
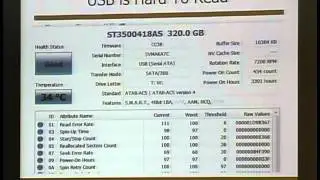
Using WinDbg to analyze our crashes
Removing bytes from your payload (such as nulls) which would prevent exploitation
Finding functions to call by walking the Thread Execution Block to find kernel32.dll's location in memory so we can call functions like LoadLibrary() and GetProcAddress()
Hashing strings to use for comparison when searching for functions, in order to minimize the size of the payload
Overwriting Structured Exception Handlers (SEH) as a means to bypass stack cookies (/GS compile option) and bypassing the SafeSEH mitigation
Overwriting virtual function table function pointers in C++ code as another way around stack cookies
Using Return Oriented Programming (ROP) to defeat Data Execution Prevention (DEP) aka non-executable (NX) stack
Using libraries which opt out of Address Space Layout Randomization (ASLR) and SafeSEH to bypass these mitigations
Using Python to mutationally fuzz the custom, never-before-analyzed, Corey's Crappy Document Format and Crappy Document Reader in order to find and exploit the numerous bugs within