Exploiting Windows Network with Responder and MultiRelay
Check this link for detailed step-by-step instructions. http://cyberthreathunt.com/2017/05/11...
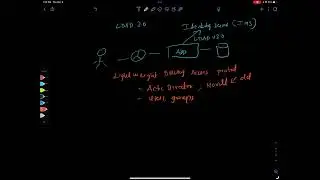
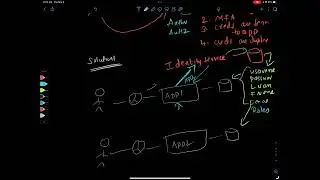
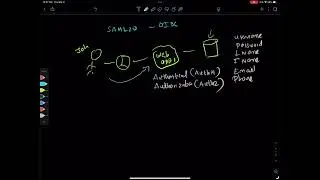
In a local network, Windows systems use Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (Net-NS) for host resolution when DNS and local hosts file lookups fail. So when a user mistypes the host name, or if a service is looking for a host which no longer exists, the queries are broadcasted to all systems in the same subnet. These protocol does not require any authentication, and any system in the local network can respond the client queries. Attackers use this very techniques to exploit systems in the local network. This is also very effective in the wireless networks which makes it a dangerous attack vector!
Responder (https://github.com/lgandx/Responder) is a tool which can be used to pull this attack. It is more of a man-in-the-middle attack where Responds the responds to client requests for SMB, HTTP, HTTPs, DNS, LLMNR, etc. and tells the systems to respond to the its own IP address. Victims in turn sends the hashes to the attacking box which could be cracked offline, or better used in SMB relay attacks where the hashes are passed to another system in the network. This tutorial will show you how to accomplish that goal.




![[FREE] Freestyle Type Beat -](https://images.videosashka.com/watch/vFyL4lyCBio)